Set Solutions CTF 2021 Week 2
Quick Navigation
Week 1
\
Week 3
\
Week 4
Nothing to See Here
Challenge description:
Nothing to See Here
Move along…
Challenge attachment: thedata.pcap
Week 2 started off relatively easy with a PCAP challenge. The first 495 packets mostly consisted of already established, encrypted TCP sessions. Starting at packet 499, a plaintext HTTP GET for the image nothing2see.jpg can be observed.
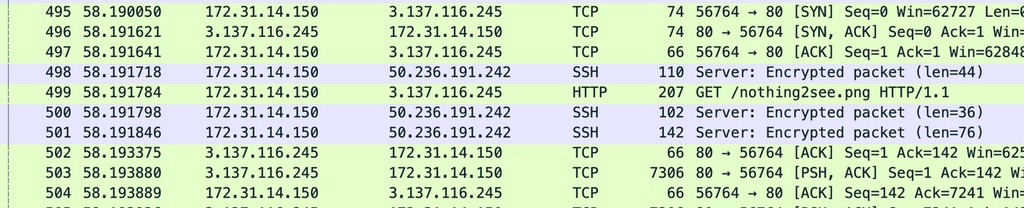
To view and export the contained HTTP objects, I selected File -> Export Objects -> HTTP, which revealed that nothing2see.jpg was the only HTTP object in the capture.
I saved and opened nothing2see.jpg, whose name and image implied a stenography challenge.
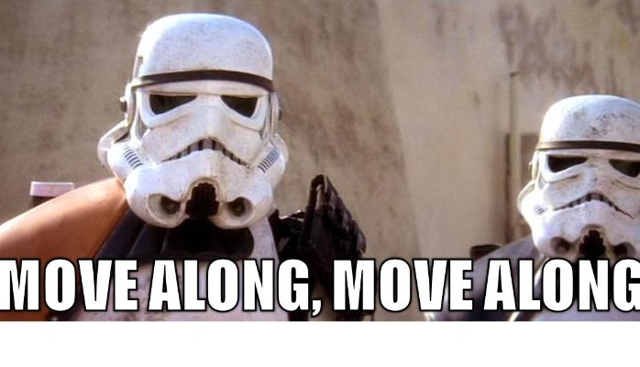
Hoping for an easy stenography challenge, I ran zsteg on nothing2see.jpg, and the flag appeared!
What is X-12?
Challenge description:
There is an asset near the Epsilon satellite referred to only as “X-12”. Chan does not have the security clearance to see what it is.
The challenge page for What is X-12 contained a button titled “Reveal Intelligence”. Upon clicking “Reveal Intelligence”, the message “You lack the clearance to access this intel brief :-(” appeared.
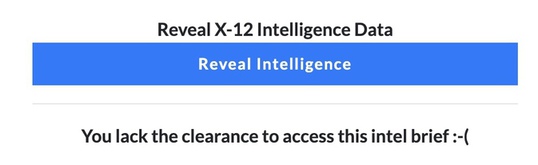
Inspection of the HTTP request for “Reveal Intelligence” revealed that isCommander was set to false. I needed to increase my clearence level by setting isCommander to True!
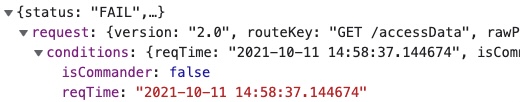
Since the request was only a GET request, I appended isCommander=True to the Reveal Intelligence endpoint. Given my corrected level of clearence, the flag was revealed!
Forgotten Password
Challenge description:
A nation-state APT group has managed to hack the admin account for our server. Unfortunately, the commander no longer remembers the password, so we can’t reset it. Perhaps we can look through the attack traffic to find it.
Challenge attachment: capture.pcap
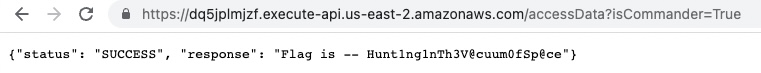
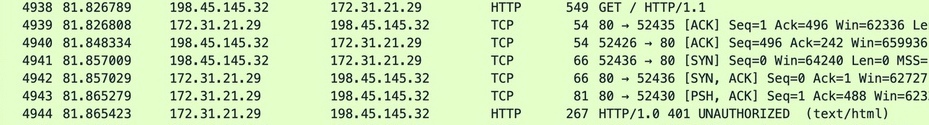
The challenge description mentions that the attached 4.1 MB capture.pcap may contain the commander’s lost logon password. Opening capture.pcap with wireshark reveals dozens of HTTP basic authentication authorization failures (response code 401).
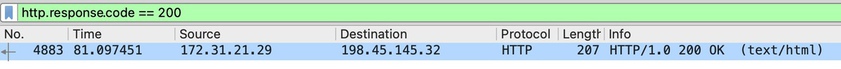
Given that the challenge asks for the correct password, we can filter for http.response.code == 200, which signifies that the page was returned normally, meaning that authentication was successful (if authentication was required). Once applied, the filter revealed a single packet with a 200 response code packet.
To view the password which resulted in the 200 response code, I right clicked on the HTTP response -> follow -> HTTP stream.
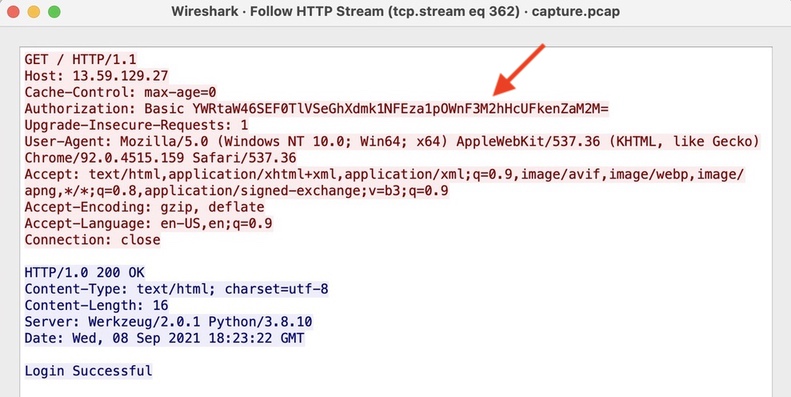
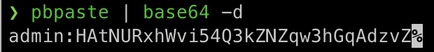
The base64-encrypted authentication credentials appeared as Basic YWRtaW46SEF0TlVSeGhXdmk1NFEza1pOWnF3M2hHcUFkenZaM2M=. Base64 decoding YWRtaW46SEF0TlVSeGhXdmk1NFEza1pOWnF3M2hHcUFkenZaM2M= using the command pbpaste | base64 -d revealed the username password combination of admin:HAtNURxhWvi54Q3kZNZqw3hGqAdzvZ3c.
Breaking and Entering
Challenge description:
Lunar shadows
Challenge attachment: file1, file2
Breaking and Entering provided two files with no additional context. Viewing file1 and file2 revealed that they were excerpts of the Unix /etc/passwd/ and /etc/shadow files, respectively.
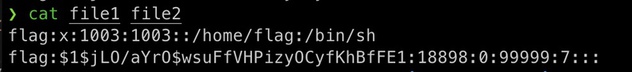
Although not needed for this challenge, I experimented with the Unix tool unshadow to merge the files.
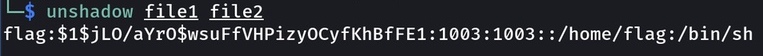
Utilizing the hash-cracking tool John the Ripper, I provided the wordlist rockyou.txt and the merged password file (file2 by itself would have also worked). I used the command john --wordlist=/usr/share/wordlists/rockyou.txt passwd.txt to begin the hash cracking process.
John finished cracking $1$jLO/aYrO$wsuFfVHPizyOCyfKhBfFE1 in six seconds, and john --show passwd.txt revealed the password didgeridoo (flag:didgeridoo:..)
Smarts vs Strength
Challenge description:
We think this might be Key to getting into the moonbase. Either you work this out xor we have to use the wrenches
Challenge attachment: SmartsVsStrength
Smarts vs Strength contained a 5 KB attachment which the Unix command file was unable to identify. However, the challenge description contained two hints, being the word Key (capitalized) and the word xor.
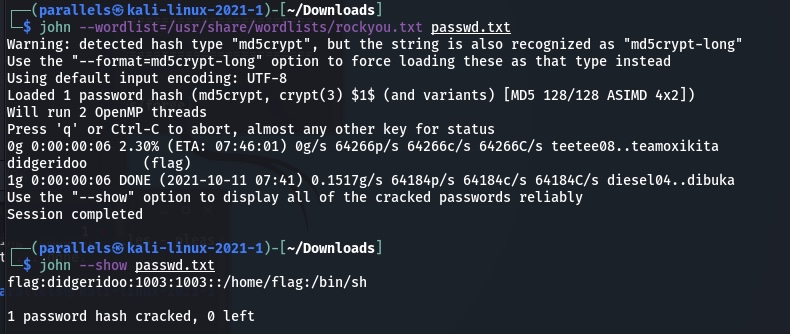
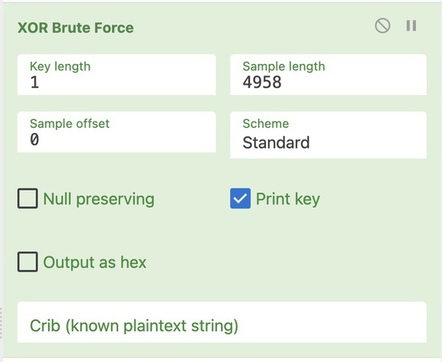
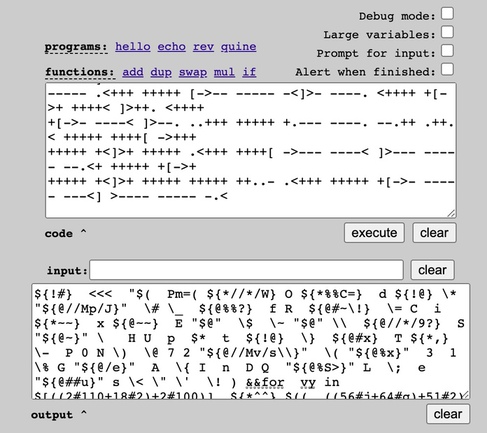
I uploaded SmartsVsStrength to cyberchef and selected XOR brute force, given the xor hint in the challenge description. The key length defaulted to 1, and I arbitrarily chose 100 as the sample length.
I searched the content of XOR’d output for the word “flag” and found a few results, which seemed to be cut off. I doubled the sample length to 200 and could now comprehend the flag-related message:
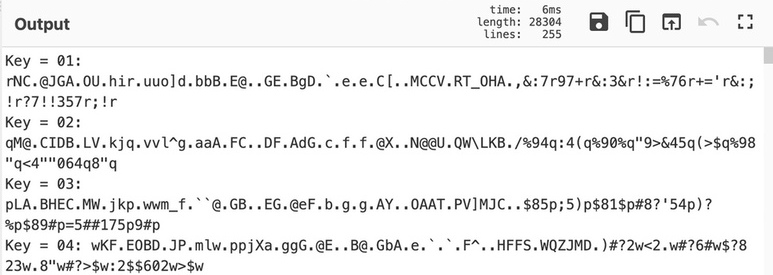
“Key = 53: …… the key that showed you this message is the character at index 0 of the flag…”
53 is hex representation of “S”, and given that other flags have been formatted as SSI{..}, it made sense that the same format would apply here.
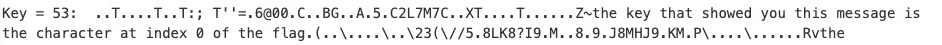
After increasing the sample length by 100 a few times and noticing that some keys were still cut off, I raised sample length to 4958, being the size of the SmartsVsStrength file. I downloaded XOR results from cyberchef, which totaled 1.3 MB.
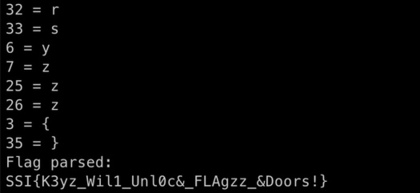
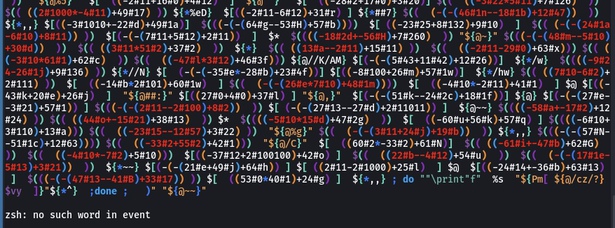
I created a python script that utilizes regex to locate each mention of “the character at index …”, parse the index, and resolve the hexadecimal value to plaintext.
import regex as re
def main():
flag_map = {}
idx_regex = re.compile(rb" character at index ([0-9]{1,2}) ")
key_regex = re.compile(rb"Key = ([0-9a-f]{1,2}):")
dat = [i for i in open("download.dat", "rb")]
for line in dat:
for idx in re.findall(idx_regex, line): # find the index in the flag
hex_key = re.findall(key_regex, line)[0] # find the key(s) corresponding to the index
flag_map[int(idx)] = bytes.fromhex(str(hex_key)[2:4]) # map the index to the key
print(f"{str(idx)[2:-1]} = {str(flag_map[int(idx)])[2:-1]}")
flag = b""
for i in range(len(flag_map)):
flag += flag_map[i]
print("Flag parsed:")
print(str(flag)[2:-1])
if __name__ == '__main__':
main()
Here is a photo of the script parsing each character and outputting the flag:
Command and Control
Challenge description:
Data being sent to a Chinese IP address from the International Space Station has been intercepted. It appears to be some kind of code.
Challenge attachment: transmission
Command and Control had a 71 KB attachment which contained non-human readable code:
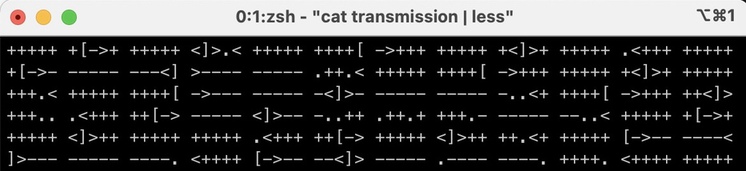
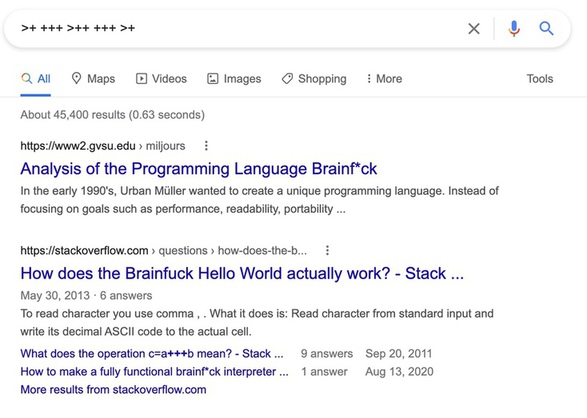
After multiple failed attempts of trying to explain the contents of transmission to google, I pasted various portions of the code directly into the google search bar. The string >+ +++ >++ +++ >+ yielded information about the programming language from the early 1990s dubbed “BrainF*ck”.
I pasted the content of transmission into a BrainF*ck interpreter1, which translated the contents to characters which appeared to be for the bash shell.
Upon pasting the translated content into Kali’s ZSH, I received the error “zsh: no such word in event”.
After too much time spent on debugging, I launched a standard bash shell by executing /bin/bash and pasted the translated message again.
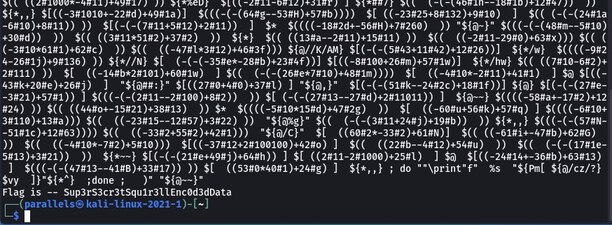
To my surprise, the shell did not throw an error, and the flag was printed!
Week 2 reflection: Overall, week 2 was more solid than week 1. Fully understanding the scope of the CTF helped with avoiding complete rabbit holes.